Remote working has introduced new security risks for contact centres. We believe security is about more than technology and policies; it’s about people. Here’s what Information Security looks like in the modern world of flexible working.
The security policies that everyone has been using for the last decade were introduced for and built around the traditional contact centre or office. These were the days when everyone worked in a restrictive environment where both physical and digital access to hardware, software and data could be minutely controlled.
Following the COVID-19 pandemic, flexible and hybrid working scenarios are likely here to stay, which means new security arrangements need to be put in place permanently. The truth is that while flexible working brings many benefits to both employees and businesses, it also comes with significant risks to Information Security (IS) that need to be managed.
In a work from home environment, there are generally more distractions and more uncontrollable factors to account for than in an office.
Last year, a survey of over 1,000 businesses reported an increase of 19% in security breaches with people working at home. Surprisingly, many of these come from former employees attempting to access resources and data they should no longer have been able to, from their personal devices.
Taking a user-focused approach to our security posture
Like all large contact centres, we have thousands of users accessing information and data, both internal and external. There are millions of points of potential risks that we must be aware of and monitor.
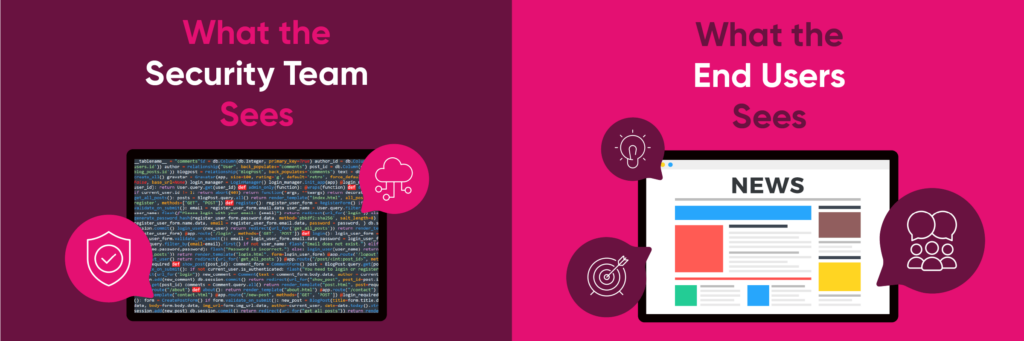
While we do implement security features such as multi-factor authentication for all devices and accounts to increase the difficulty for anyone with malicious intent trying to breach our systems, what many people don’t realise is that it is often the non-malicious and unaware user that is the weakest layer in the security system.
You can invest millions in a security infrastructure, but all it can take is a slip by one inattentive user for hackers to gain access of your systems. For example, organisations often focus on confidential information and where it is stored, but there could be cases where a breach occurs via third-party software installed on a company device or an employee’s device.
To prevent all possibility of breaches it is not enough to just have information security policies; we have to educate our people too.
Finding it difficult to integrate security into business functions? Here’s how we think information security should enable the business to innovate and do more.
Managing users and user behaviour is key
In a modern distributed contact centre, or similar virtual working environment, security policies must focus on instilling and reinforcing correct user behaviour.
The first step is to ensure that a culture of security awareness permeates throughout the organisation. Most commonly this starts with senior management, whose job it is to lead by example and secure buy-in from all employees. This starts during the onboarding process from the moment an employee joins the company.
Ultimately everyone in the organisation who enters the building or interacts with company systems and data is responsible for ensuring security standards are met. Are your employees able to spot a phishing email and take appropriate action? Do they know basic password best practice? Do they understand that data, such as large files, should be encrypted when in transit, whether it’s been sent internally or externally? Do they know how to properly secure their home wi-fi and personal devices that might be accessing the same network as work devices? And finally, when they do encounter suspicious activity, do they know how to report it and to whom?
In another recent survey by ZDNet, 52% of employees said that when working from home they felt they could get away with things like not using encryption for sharing confidential files. In the same survey, half the respondents said they had had to find a way around security features to get their usual work done efficiently. This demonstrates how important it is for security processes to be fit for purpose in the real world so that they do not become a barrier for remote and homeworking employees.
Education is an important component of this. Which doesn’t just mean training employees in best practice policies and security systems. It’s rather about instilling and reinforcing good habits and developing a broad understanding that information security is no longer just about localised IT security. Security breaches don’t just happen on work devices. Particularly when working remotely, personal devices can be a point of weakness, as can logging on to a public wi-fi.
It’s up the employer to help guide employees on their use of technology beyond the workspace so that they know what to look out for.
User-centric processes and systems
In most offices and contact centres, people have different tasks and therefore different requirements for how they go about getting their work done. Everyone also takes in information differently. Some people might form a habit immediately, while others need frequent reminders or prompts.
One-size fits all policies just won’t cut it. Neither will blaming humans for being human and making mistakes from time-to-time, which is not conducive to a great work culture either. What’s important is to understand how your users and employees best consume information and provide them with as much help as possible to avoid accidents.
For example, a simple red tag to show an email is coming from an external source keeps users aware that, for example, if it’s an internal request with an external notification, there is a discrepancy.
Another example that worked with one our clients, was the creation of videos to present snippets of information on security hygiene. Over time this drip feeding of information, without overwhelming people, garnered more engagement than full-length reports or dry instructional emails.
Finally, the ensemble of technologies, policies, and directives that make up your information security need to be constantly evolving. As new iterations of hardware and software come online, as job roles and working conditions continue to change, and as new cyber-security threats continue to emerge, you need to be constantly reviewing the measures you have in place.
That’s why at TSA Group, we are ISO27001 Certified, not only to be compliant with regulatory requirements but also to maintain a competitive edge by ensuring our Information Security processes are always fit for purpose in an ever-changing landscape.
What best practice looks like
First of all, you will already have in place basic security measures like multi-factor authentication, password best practice, data encryption in storage and in transit, and tight policies on using personal devices and public networks. Nothing is “Set & Forget”.
The next step is to foster a culture of security awareness that gives workers regular reminders and prompts to follow best practice, and get them to develop a security conscious mindset where they pay attention to suspicious activity and do not see security as a barrier to getting work done.
Neither can users afford to allow their information security knowledge to become out of date, as things change so quickly. Nor should they get into the mindset that information security is solely the responsibility of the IT department.
Organisations need to create processes and build systems that cater for how their users work today and in the future. The goal is to educate your employees to protect themselves, whilst also protecting your organisation.
TSA are Australia’s market leading specialists in CX Consultancy and Contact Centre Services. We are passionate about revolutionising the way brands connect with Australians. How? By combining our local expertise with the most sophisticated customer experience technology on earth, and delivering with an expert team of customer service consultants who know exactly how to help brands care for their customers.